Get Started
Graphite's supplier management tool helps you onboard faster, cut time on risk reviews and streamline supplier validations. Save time and money.
Mastering the Third-Party Risk Management Lifecycle in 2026
Your business now runs on a web of vendors, partners, cloud services, and contractors. That reach creates leverage, but it also expands your attack surface and operational exposure. Many risk leaders already rank third-party risk among the top five threats to growth. The uncomfortable truth: reputational damage often begins in a system you don’t control.
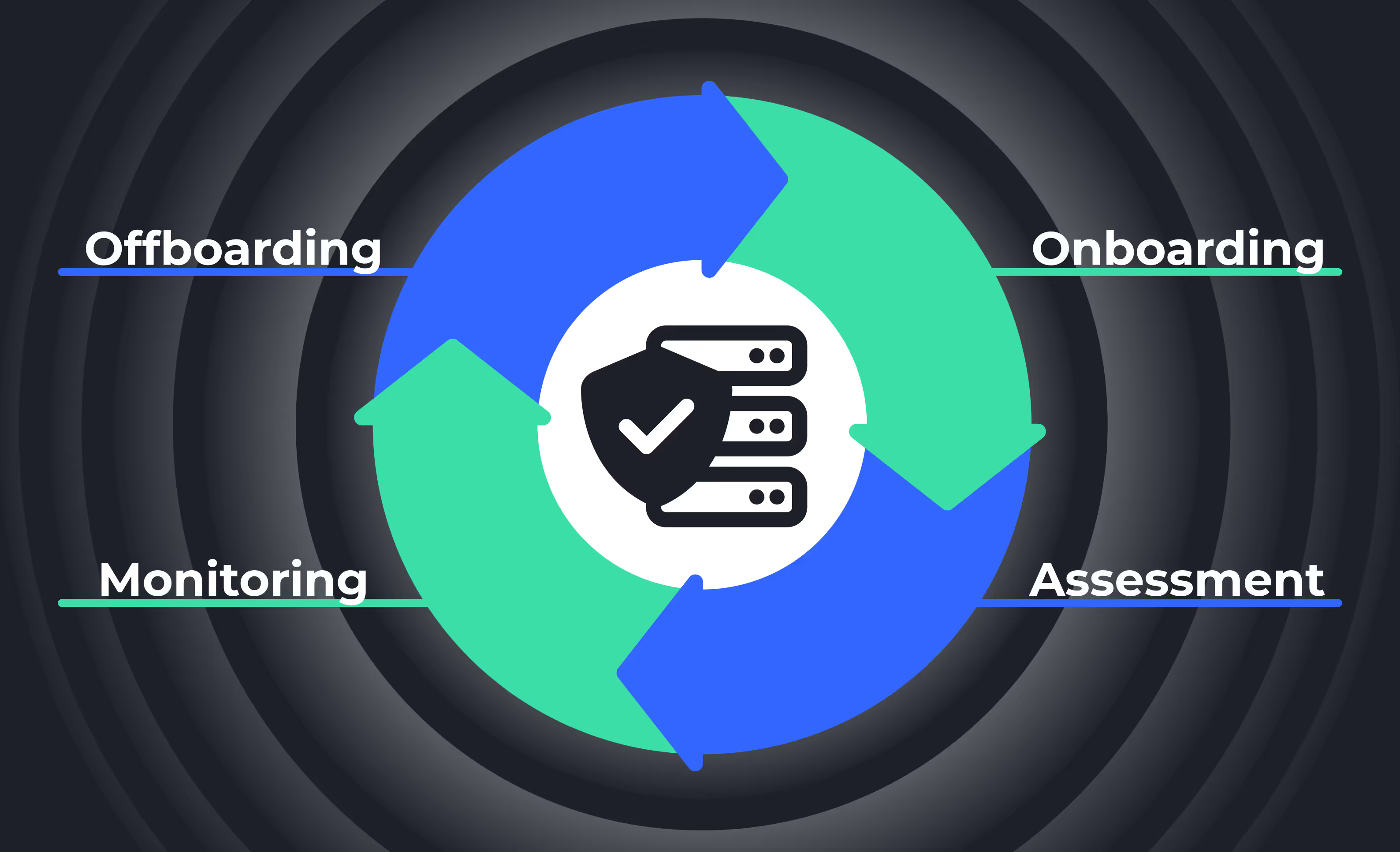
That’s why Third-Party Risk Management (TPRM) has to be more than paperwork. Done right, it’s a repeatable operating model that identifies, assesses, monitors, and mitigates risk across every external relationship without slowing the business down. In this guide, we lay out a practical lifecycle you can run, measure, and improve.
The Diverse Risk Landscape (and why a lifecycle matters)
As your third-party network grows, so do the ways risk can creep in. The categories are familiar, but their triggers are not always obvious:
- Cybersecurity risk: A vendor’s weak controls can extend your attack surface and lead to breaches, penalties, and brand damage.
- Operational risk: Disruptions in a supplier’s processes or their upstream dependencies can stall your delivery and add cost.
- Financial risk: An unstable provider can miss commitments or fail entirely, putting revenue and continuity at risk.
- Regulatory & compliance risk: If a third party misses a standard or regulation, liability can land on you, even when you weren’t directly involved.
Because these risks can surface at any point in the relationship, a lifecycle approach, not a one-time assessment, keeps you consistently vigilant. Each stage has a clear purpose, owner, and evidence trail, so issues are caught early and decisions are defensible later.
With the “why” established, let’s shift to the “how.” The fastest way to build momentum is to standardize the path every third party follows. This process can be broken down into seven distinct phases.
7 Phases of a Third-Party Risk Management Lifecycle
Phase 1: Planning & Third-Party Identification
Set the foundation before you collect evidence. Define risk criteria (what matters and how much), your risk appetite (what you can tolerate), and roles across Procurement, Security/Privacy, Legal, Finance, and the business owner. Then build a real inventory, not a spreadsheet you update once a year, but a living list of vendors, services, and relationships you can segment by criticality.
Early screening against sanctions, enforcement lists, and known red flags helps you rule out relationships that are too risky to start. With a clean inventory and clear criteria, you can size the effort for each vendor rather than treating them all the same.
Phase 2: Risk Tiering & Materiality
Tiering converts judgment into a consistent policy: critical/high/medium/low, driven by data sensitivity, operational dependency, regulatory scope, geography, and financial exposure. The output isn’t just a label; it sets the depth of due diligence, who needs to review, and your SLA targets for approval.
Tiering is where scalability begins: high-risk vendors get deeper scrutiny; low-risk vendors move quickly with proportionate checks. Once the tier is set, you can right-size diligence and move directly into evidence collection.
Phase 3: Due Diligence & Validation
Diligence should be thorough, tier-based, and free of busywork. Use standardized, dynamic questionnaires for security, privacy, business continuity/disaster recovery, financial health, and ESG/modern slavery. Collect validations that matter: insurance certificates, SOC/ISO attestations, tax and banking confirmation, sanctions/PEPs screens, and data protection commitments where personal data is in scope (GDPR, CCPA, etc.).
Keep a findings register that captures gaps and strengths, and track which controls you need to see improved before approval. Efficiency matters here. If you can leverage pre-completed evidence from trusted exchanges or reuse prior questionnaire answers from a vendor’s existing profile, do it. The goal is clarity with speed, not friction for its own sake. Evidence without action doesn’t reduce risk, so diligence must feed a crisp decision.
Phase 4: Risk Treatment & Approval
Every finding needs a path to closure. Classify gaps (high/medium/low), set CAPAs with owners and deadlines, and align remediation to your risk appetite. For each relationship, choose to accept, mitigate, or avoid gate approval for the necessary CAPAs to be accepted and tracked.
Document the rationale, especially when you accept risk, so future audits and reviews see the context, not just the outcome. With the decision made, it’s time to make those controls binding and transparent.
Phase 5: Contracting & Formalized Onboarding
Contracts are where risk management becomes enforceable. Translate risk into clauses: audit rights, breach notice windows, subcontractor controls, data residency, encryption/MFA, insurance levels, and termination rights. Keep a clause library mapped to risk categories and tiers to avoid “shadow” language that dilutes protections.
Onboarding should be risk-aware and documented. Track who’s responsible on both sides, what data and systems are in scope, service definitions and SLAs, and escalation paths. Maintain a single record of what access is granted to whom, by when, and under what conditions. This makes later monitoring and offboarding clean.
With the contract signed and onboarding complete, vigilance shifts from “prove capability” to “prove it stays in place.”
Phase 6: Ongoing Monitoring & Incident Management
Assessment is a moment in time; risk changes constantly. Set a monitoring cadence by tier. Keep documents current (insurance, certifications), watch for control drift (new subprocessors, new data categories), and monitor financial health, adverse media, and sanctions updates. Track performance SLAs alongside risk controls as both drive business impact.
When incidents happen, act fast: triage severity, notify per contractual and regulatory timelines, contain the issue, and open CAPAs with retesting on closure. Use KRIs (key risk indicators) to catch rising risk early, and trigger targeted reassessments when facts change (scope, geography, data flows, or material incidents).
Phase 7: Termination & Offboarding
A secure exit is non-negotiable. Revoke all access (human and non-human), retrieve or erase data, collect final attestations, and return/destroy assets as required. Close the loop in your inventory: mark status, update retention schedules, and record evidence of each step.
Offboarding is where many programs stumble; a checklist with system-enforced steps keeps you compliant and makes audits straightforward. With the lifecycle in place, the next step is tuning scope and scale so the program stays fast where it can and deep where it must.
Tailoring Scope, Scale, and Risk-Based Depth
No two organizations share the same risk appetite or resource constraints. A strong TPRM lifecycle is flexible by design. Here’s how to align a standard TPRM lifecycle to your organization’s needs:
- Align to appetite: Calibrate stages and controls to your tolerances and industry obligations.
- Tier for efficiency: Focus scrutiny on critical and high-risk vendors; keep low-risk paths lean.
- Account for complexity: Service type, geography, data sensitivity, and integration depth should influence assessment rigor.
- Work within capacity: Smaller teams benefit most from automation. Reduce manual steps and enforce the process with workflows and alerts.
- Keep it living: Update the program as threats evolve, operations change, and lessons emerge from incidents or audits.
The practical test: If your team can explain the “why” behind stage depth in one sentence and the evidence is easy to find, you’ve sized it well.
Tailoring is easier and safer when the program is powered by automation instead of ad-hoc emails and spreadsheets.
Where Graphite Connect Fits (supplier-first, audit-ready)
You bring the categories, policy, and business judgment. Graphite provides the rails so the lifecycle runs fast and clean with:
- Guided intake & auto-tiering: Collect what matters up front and size reviews by risk. No guesswork, no redundant asks.
- Built-in validations & expiry alerts: Tax/banking/insurance checks, sanctions/PEPs, and ESG attestations run continuously; expirations notify stakeholders before they become findings.
- Versioned supplier profiles: Eliminate duplicate requests; keep a living record of answers and changes.
- Workflow orchestration with SLAs: Procurement, Legal, InfoSec, and Finance can be engaged when needed in your fully automated process, with transparency around share one queue with owners, due dates, and time-stamped approvals.
- Contract & renewal visibility: Clause requirements tie to risk tier; reminders prevent rollovers and keep obligations monitored in real time.
- Scorecards & monitoring: Delivery, quality, responsiveness, and document health roll into QBR-ready views so actions have owners and deadlines.
- Integrations that stick: ERP/CLM/IDP/TPRM connectivity keeps spend and access gates aligned with risk decisions—no re-keying, no drift.
When the program is supplier-first and audit-ready by default, you move faster with less risk, and your evidence is ready when asked.
Put Your TPRM Lifecycle on Rails
A modern third-party risk management lifecycle doesn’t trade speed for safety. With clear stages, proportionate depth, and automation where it counts, approvals become predictable, monitoring stays continuous, and audits turn into reviews, not rescue missions. If you’re ready to see how Graphite streamlines intake, tiering, due diligence, approvals, monitoring, renewals, and exits, schedule a demo and make your TPRM lifecycle run itself, so your team can focus on decisions, not administration.